Sustainability
TechLab
Where Climate Technology Meets Data Innovation
SocialLab
Navigating the Interplay of Society and Media.
ClimateLab
The hub where innovation converges with environmental responsibility
Volunteer
We offer many voluteering opertunities in our Tech, Social and Climate Labs

Get Involved With Social Climate Tech
Engage with us and learn new things.
TechLab
ClimateLab
SocialLab
Volunteering



We are proud to be at the forefront of innovation in the field of social climate tech, and we are dedicated to using the latest technologies to create a more sustainable future for all. Whether it's through our cutting-edge research, our education initiatives, or our partnerships with organizations around the world, we are committed to using technology to drive progress and make a real impact.
Latest from Social Climate Tech News
We build tools to give you the option to decide how much information you need to know.

Revolutionizing Tech with Sustainable AI Engineering
Unveiling a Green Tech Revolution: Sustainable AI Engineering
Imagine a world where technologists aren't just designing AI models...
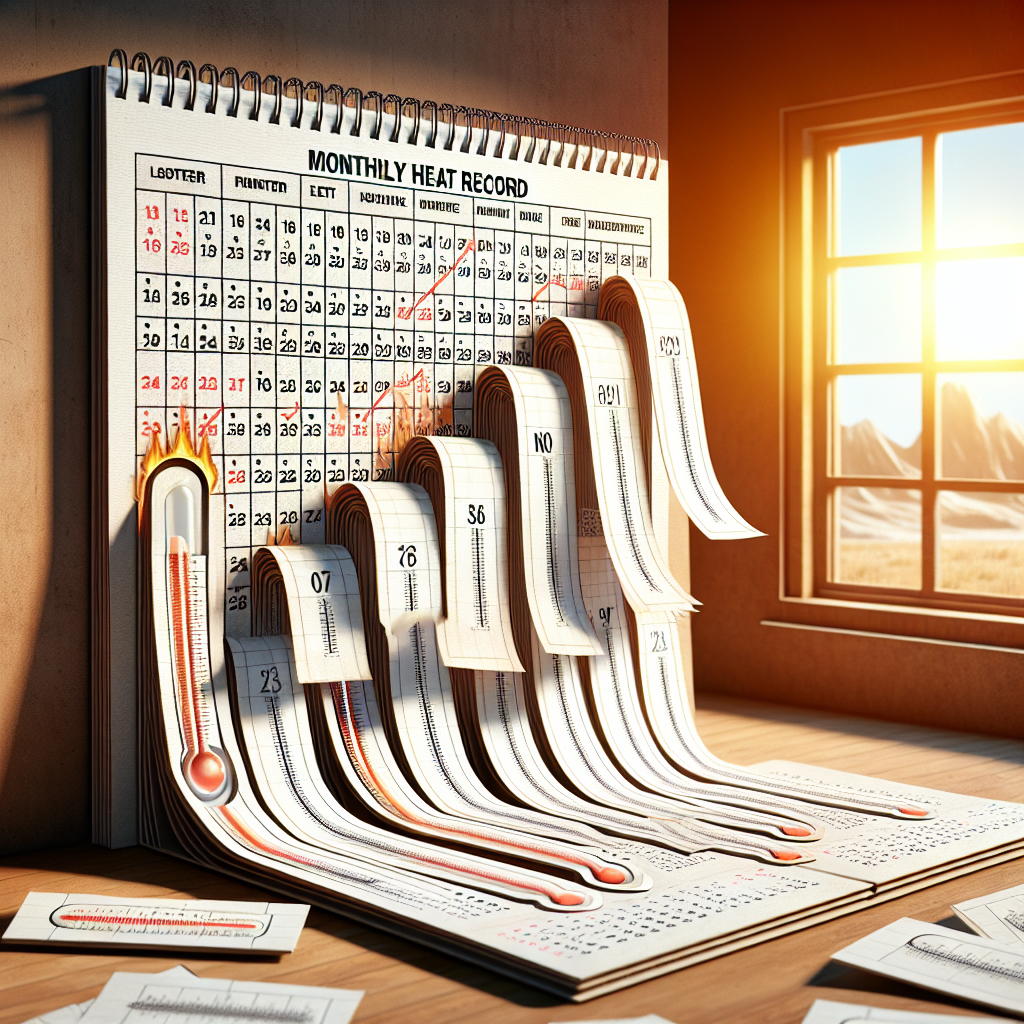
Tenth consecutive monthly heat record
Staggering statistics reveal that March brought us the 10th consecutive global heat record, with temperatures surging 0.1C higher than the...

Navigating the Complexities of Software Environments
In the dynamic realm of software development, the transition from one company to another is often akin to stepping into an entirely different...

Spotting Fake Knowledge in Software Development
The internet democratized information access. Anyone can delve into seemingly complex topics, leading to a phenomenon called the "shortcut...